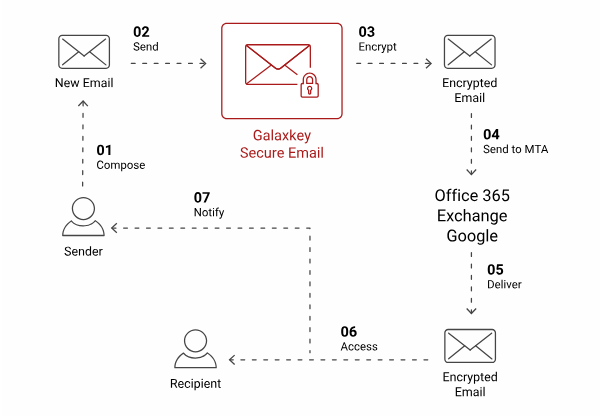
Secure Emails
Identity-Based Encryption secures messages at content level. | Protection remains in place before, during, and after delivery. | Administrators can define and enforce usage policies centrally.
Learn MoreIn the cybersecurity sector, service excellence means proactively defending your infrastructure, data, and people — before threats materialise.



Welcome to Dinola Tech+
We deliver integrated Security Solutions, Data Protection solutions, ISO certification and consultancy, and ICT Training in one place.
You get enterprise-grade cybersecurity, structured data protection, ISO compliance support, and practical skills development—aligned to your business needs and delivered as a single, coordinated offering.
Enterprise Data Protection
We deliver enterprise-grade encryption that keeps you in control of your data at rest and in transit, while supporting regulatory and operational requirements.
Identity-Based Encryption secures messages at content level. | Protection remains in place before, during, and after delivery. | Administrators can define and enforce usage policies centrally.
Learn More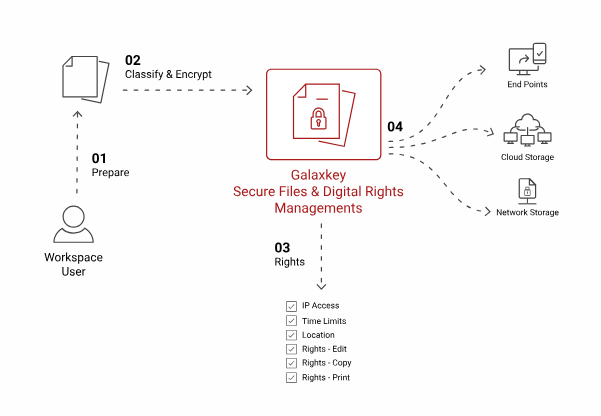
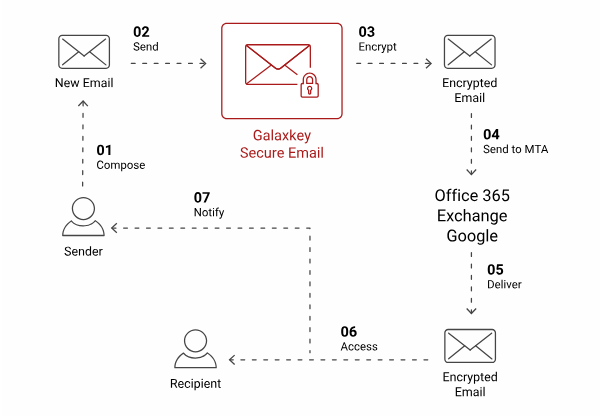
Define who can access files. | Control when, how, and from where access is permitted. | Revoke access instantly, even after distribution.
Learn More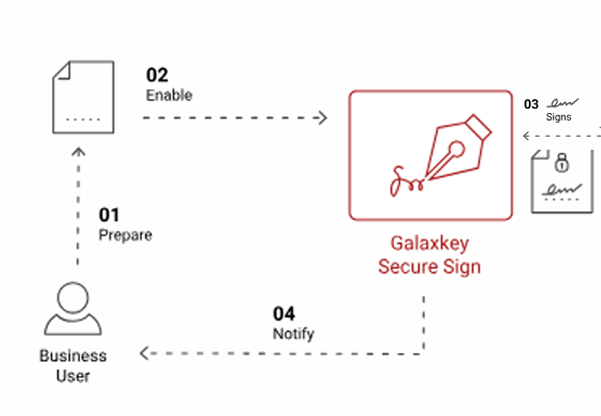
Legally binding digital signatures. | Configurable approval workflows. | Full audit trail for verification and compliance.
Learn More
Files remain encrypted in storage and during transfer. | You control who can view, edit, share, or revoke access. | Full audit logs track all user activity for compliance and oversight.
Learn More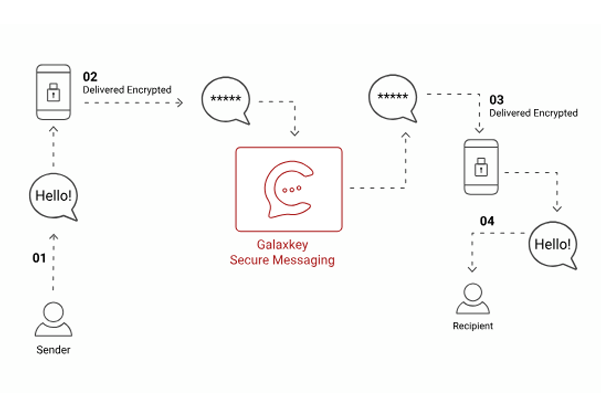
Encrypted instant messaging. | Message recording and audit capability. | Centralised administrative control.
Learn More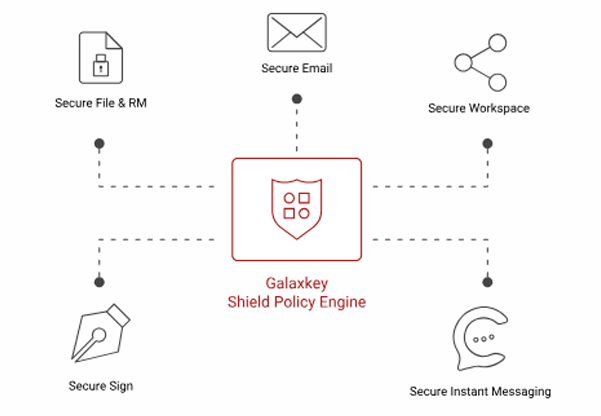
Enterprises handling sensitive data require full control, visibility, and compliance without exposing files to the cloud.
Learn MoreAdvisory and Certification Services
Our Regulatory Compliance Advisory and Certification services are designed to reduce regulatory risk, accelerate certification timelines, and embed compliance into business operations. We act as a single trusted partner throughout the entire compliance lifecycle – from advisory and readiness to certification and ongoing sustenance.
From choosing an ISO standard to managing your certification, we can support you with all your ISO needs.
Learn More →Get support with accredited certification like UKAS, upgrade to a new ISO standard and more with bespoke consultancy services.
Learn More →We offer a range of engaging and interactive training options to suit your individual learning needs.
Learn More →Our Regulatory Compliance Advisory and Certification services are designed to reduce regulatory risk, accelerate certification timelines, and embed compliance into business operations. We act as a single trusted partner throughout the entire compliance lifecycle – from advisory and readiness to certification and ongoing sustenance.

Our team holds CISSP, CISM, CEH, and ISO lead auditor certifications. Every engagement is led by practitioners with deep, hands-on expertise across industries.
We support over 50 international and regional compliance standards across information security, privacy, quality, environment, business continuity, and industry-specific regulations. Key standards include:
